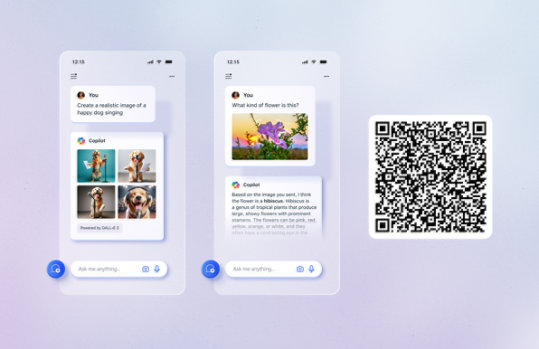
Unlock your potential with Microsoft Copilot
Get things done faster and unleash your creativity with the power of AI anywhere you go.
Windows Server 2003/2003 R2 Retired Content
Windows Server 2003, Windows Server 2003 SP1 and SP2, and Windows Server 2003 R2 retired content. The content you requested has already retired. It's available to download on this page.
Important! Selecting a language below will dynamically change the complete page content to that language.
Version:
1.0
Date Published:
7/18/2016
File Name:
Windows Server 2003_en-us.pdf
File Size:
147.6 MB
Complete set of content formerly published at Windows TechNet for Windows Server 2003, Server 2003 Service Pack 1 and 2, and Windows Server 2003 R2. Includes all content shipped in the Windows Server 2003 product, along with content concerning Operations, Security and Protection, Technical Reference, Glossary, System Requirements, Getting Started, Planning and Architecture, and Deployment. Also includes technical library content for Windows Server 2003 Service Pack 1 and 2. For Windows Server 2003 R2, content includes Installation, Product Evaluation, Getting Started, Planning and Architecture, Deployment, and content included in the product.Supported Operating Systems
Windows 2000, Windows Server 2003, Windows XP
Any application capable of displaying PDF files- The download is a pdf file. To start the download, click Download.
- If the File Download dialog box appears, do one of the following:
- To start the download immediately, click Open.
- To copy the download to your computer to view at a later time, click Save.
